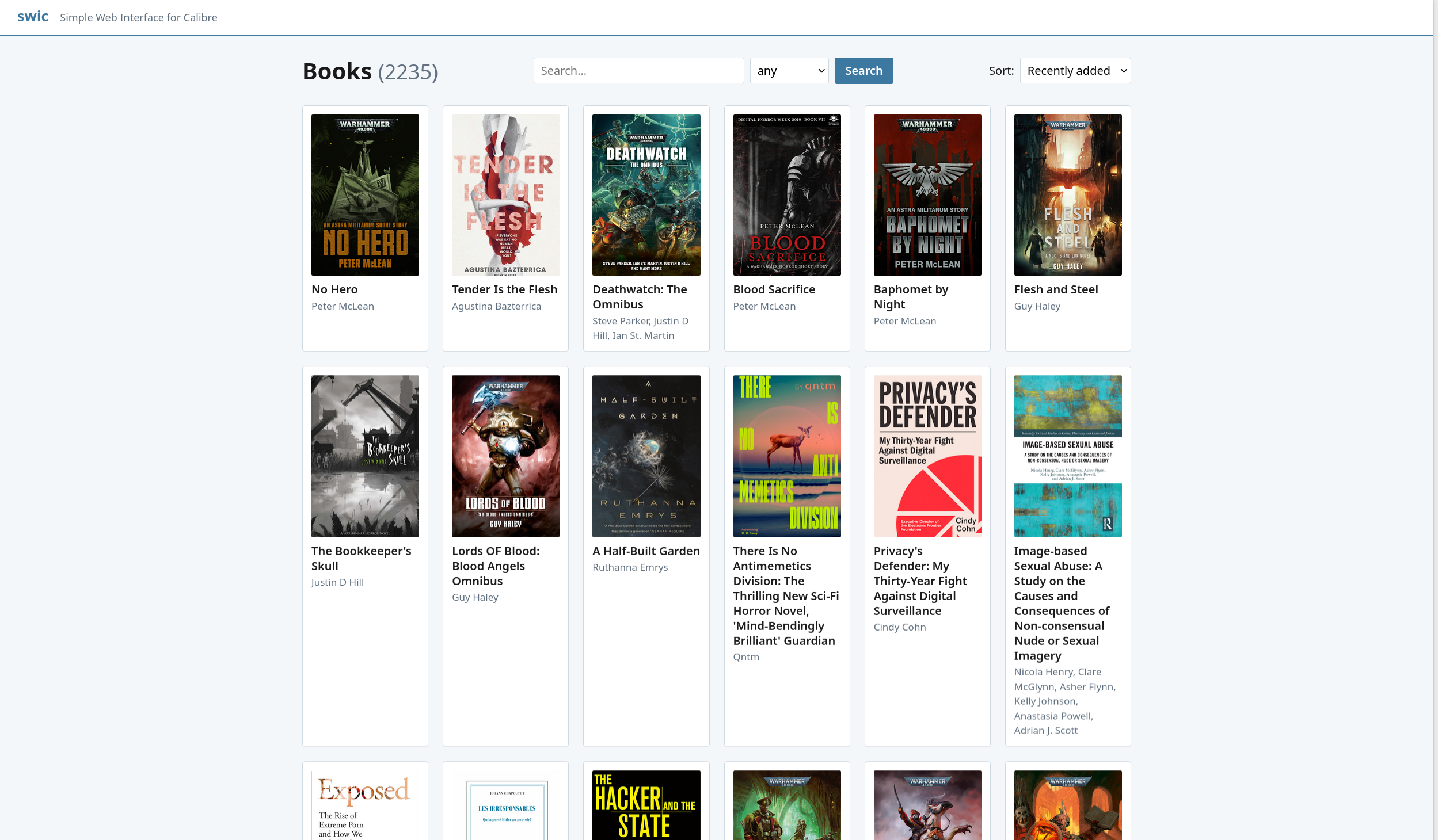
I'm ~regularly doing lightweight security audits of the services I'm running exposed on the internet. One of them is calibre-web. After 2h and 17 security-related pull-requests later, I gave up and decided to write a replacement: swic. It only has 3 user-facing features: showing the ebooks as a list, a searchsbar, and allowing the user to download the ebooks. I don't need anything else. UI-wise, it looks like this:
It's written in go, meaning that it's both trivial to deploy and to audit. It
has a single direct dependency
(modernc.org/sqlite) to read calibre's database.
It doesn't handle users, doesn't need to have write-access to anything, doesn't
process untrusted data besides user-provided urls, makes use of Go's
os.root to prevent path traversals. The
interface is fully responsive and doesn't use any javascript.
The code isn't the prettiest, but the whole thing was written in an evening. You should replace calibre-web with it before somebody drops an RCE :p